The FBI wants the public to help it track down Chinese hackers
published 6 November 2024
Agency is asking anyone with information to reach out

- FBI publishes a call to arms, asking for the public’s help
- The group(s) have been targeting government edge devices for years
- Multiple groups seem to have been involved
The US Federal Bureau of Investigation (FBI) is asking the general public for help in the investigation, and identification, of a threat actor targeting edge devices and computer networks in government entities and other companies.
Citing a report from cybersecurity researchers Sophos, the FBI said an Advanced Persistent Threat (APT) group created and deployed malware “as part of a widespread series of indiscriminate computer intrusions” built to steal sensitive information from firewalls worldwide.
The campaign leveraged, first and foremost, CVE-2020-12271, an SQL injection issue found in SFOS 17.0, 17.1, 17.5, and 18.0 before late April 2020, on Sophos XG Firewall devices. The vulnerability affected devices configured with either the administration (HTTPS) service or the User Portal exposed on the WAN zone. The crooks abused the bug to trigger remote code execution (RCE), leading to the exfiltration of usernames and hashed passwords from local device admins, portal admins, and user accounts.
Years-long campaign
The move is linked to a series of recent reports from Sophos which details multiple hacking campaigns that took place between 2018 and 2023 and apparently exploited edge infrastructure appliances to deploy custom malware. Sophos dubbed the campaign Pacific Rim, and attributed it to multiple Chinese state-sponsored threat actors, including the infamous Volt Typhoon.
Sophos also said that CVE-2020-12271 wasn’t the only vulnerability exploited in this campaign, also listing CVE-2020-15069, CVE-2020-29574, CVE-2022-1040, and CVE-2022-3236.
“From 2021 onwards the adversaries appeared to shift focus from widespread indiscriminate attacks to highly targeted, ‘hands-on-keyboard’ narrow-focus attacks against specific entities: government agencies, critical infrastructure, research and development organizations, healthcare providers, retail, finance, military, and public-sector organizations primarily in the Asia-Pacific region,” the company said at the time.
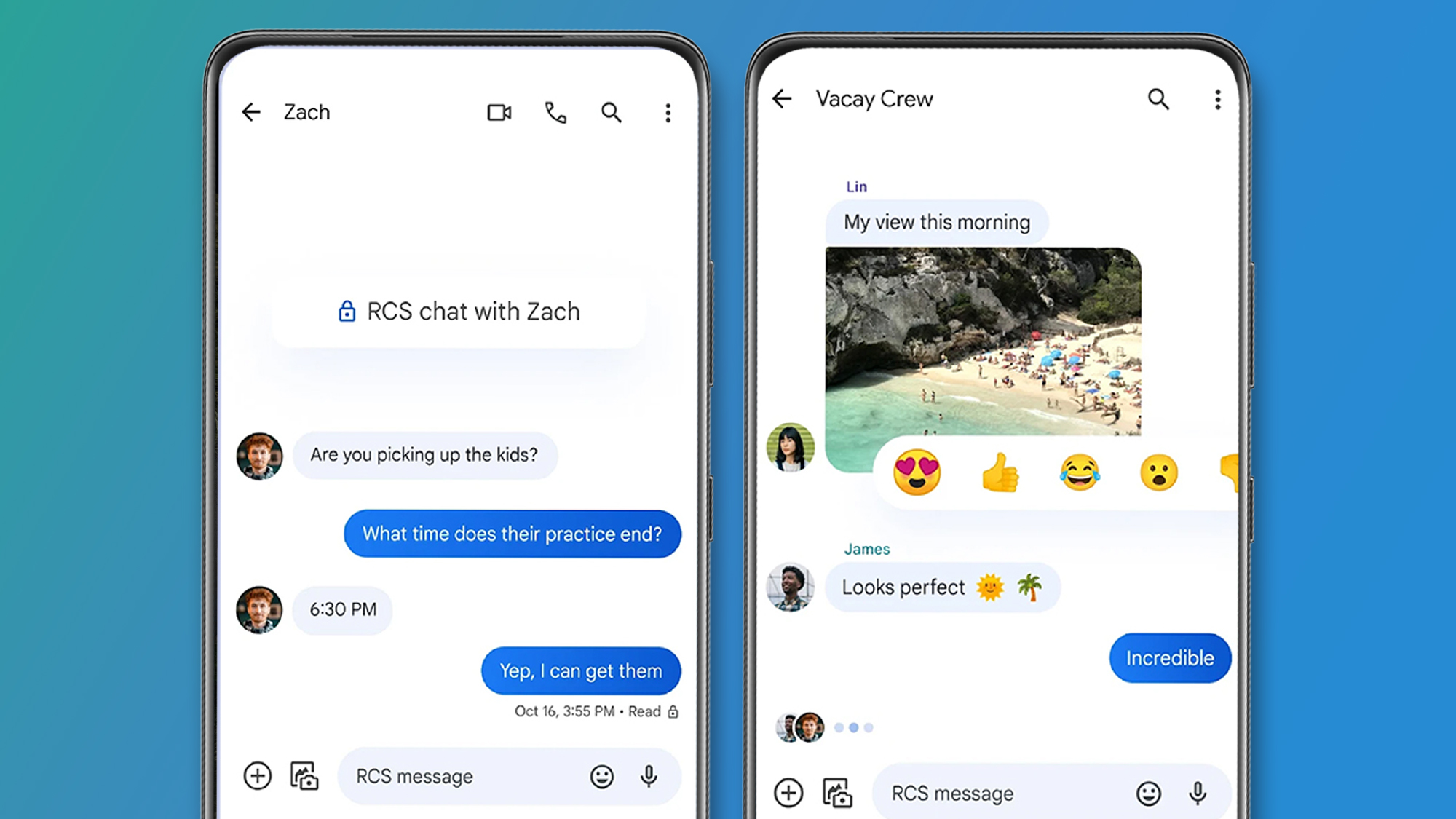
Those with actionable intel can reach out to the FBI via WhatsApp, Signal or Telegram.
Are you a pro? Subscribe to our newsletter
Sign up to the TechRadar Pro newsletter to get all the top news, opinion, features and guidance your business needs to succeed!
Via The Hacker News
You might also like
- Volt Typhoon is actually a CIA asset, China claims
- Here’s a list of the best firewalls today
- These are the best endpoint protection tools right now
Sead is a seasoned freelance journalist based in Sarajevo, Bosnia and Herzegovina. He writes about IT (cloud, IoT, 5G, VPN) and cybersecurity (ransomware, data breaches, laws and regulations). In his career, spanning more than a decade, he’s written for numerous media outlets, including Al Jazeera Balkans. He’s also held several modules on content writing for Represent Communications.

Singtel targeted by Chinese hackers in “test run” for attacks on US targets

Hundreds of malware-laden fake npm packages posted online to try and trick developers

Apple’s next-gen iMac 24-inch could get a much-wanted upgrade for the screen (though maybe not the one you want)
Most Popular








-
 1Apple’s next-gen iMac 24-inch could get a much-wanted upgrade for the screen (though maybe not the one you want)
1Apple’s next-gen iMac 24-inch could get a much-wanted upgrade for the screen (though maybe not the one you want) -
2Everything worth buying in the Currys Black Friday sale – the 23 best deals picked by a Black Friday expert
-
3The Kindle Colorsoft faces shipping delays, but don’t be put off by its yellow screen issue
-
4Singtel targeted by Chinese hackers in “test run” for attacks on US targets
-
5Time Cut is Netflix’s #2 movie but it’s not worth your time – here are 3 better sci-fi horrors with over 88% on Rotten Tomatoes





